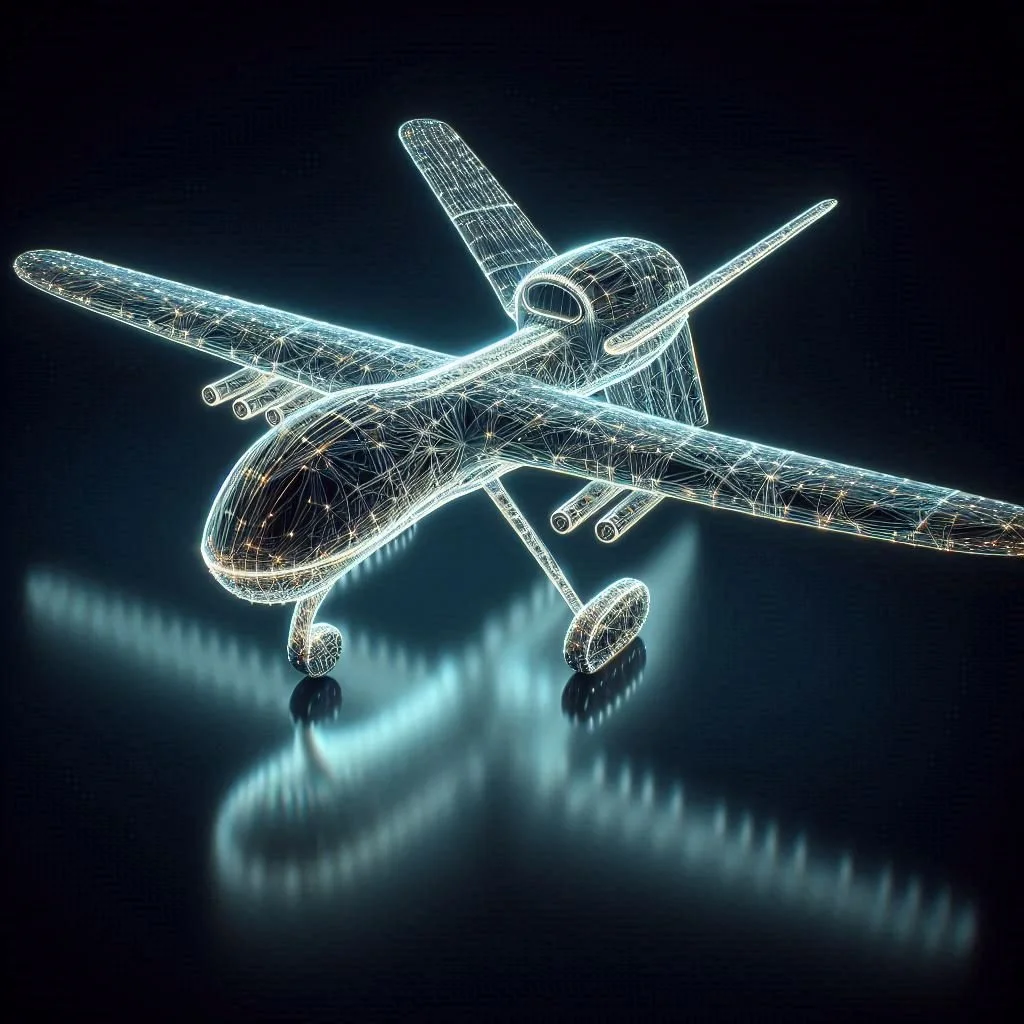
UAV Data Security
XQ is a Zero Trust Data Security platform designed to protect sensitive information at the data layer—independent of devices, networks, or infrastructure. For drone programs, XQ enables mission-critical data (telemetry, video feeds, command and control signals, and payload data) to be cryptographically secured, policy-bound, and access-controlled in real time. This ensures that only authorized users and systems can access or act on data, even in contested, disconnected, or multi-domain environments. XQ integrates seamlessly into existing drone architectures, providing data-level protection, key localization, and granular governance without disrupting operations or performance. XQ’s partnership with Qrypto Trust brings pioneering Zero Trust PQC certificate exchange.
Capabilities- The collections streams from Unmanned Aerial Vehicles (UAVs) can indicate the skew and zoom capabilities. The raw feeds need to be PQC encrypted to protect this information but the PQC is often too bulky to be a reasonable solution. Our optimization and acceleration minimizes latency making ZAP suitable for 8k streaming.
Collections- Compiled data often exceeds the classification of the host system when considered as one group of information/intelligence. Data at rest before exploitation or resultant products need to be secured as they are collected and produced.
Protection- The UAS itself requires protection from cyber-intrusion vectors that could compromise the integrity of the system, or in some demonstrated circumstances pirate the entire system. Unsecured data links and identity spoofing are risks that have been used on more than one occasion to our adversary's advantage.
Here are several cyber security considerations.
The obvious is cybersecurity with zero-trust, zero intermediary knowledge, and edge generated keys meaning the network/cloud/servers never handle the private key or "see" the encrypted contents as they exchange. This also applies to data at rest being protected.
Meta tagging embeds the classification for control, supports hi/low and low/hi transfer mechanisms, and supersedes password/group permission compartmentalization. The largest and most damaging leaks have been from IT professionals who abused their credentials.
Meta tagging also has a counter-intel role in providing information of unexpected access points and intrusion vectors for active prevention and follow on actions.
There is a risk reduction in information sharing via one-way bridges with applied filtering, PQC encrypted data transfers, and PQC encrypted data at rest that maintains data sovereignty through key controls in the case of partner nation political, military, or economic collapse/realignment.
PQC Visualizer
https://www.qryptotrust.com/pqc-visualization
Papers on secure drone communications we authored with the Idaho National Lab